TL;DR
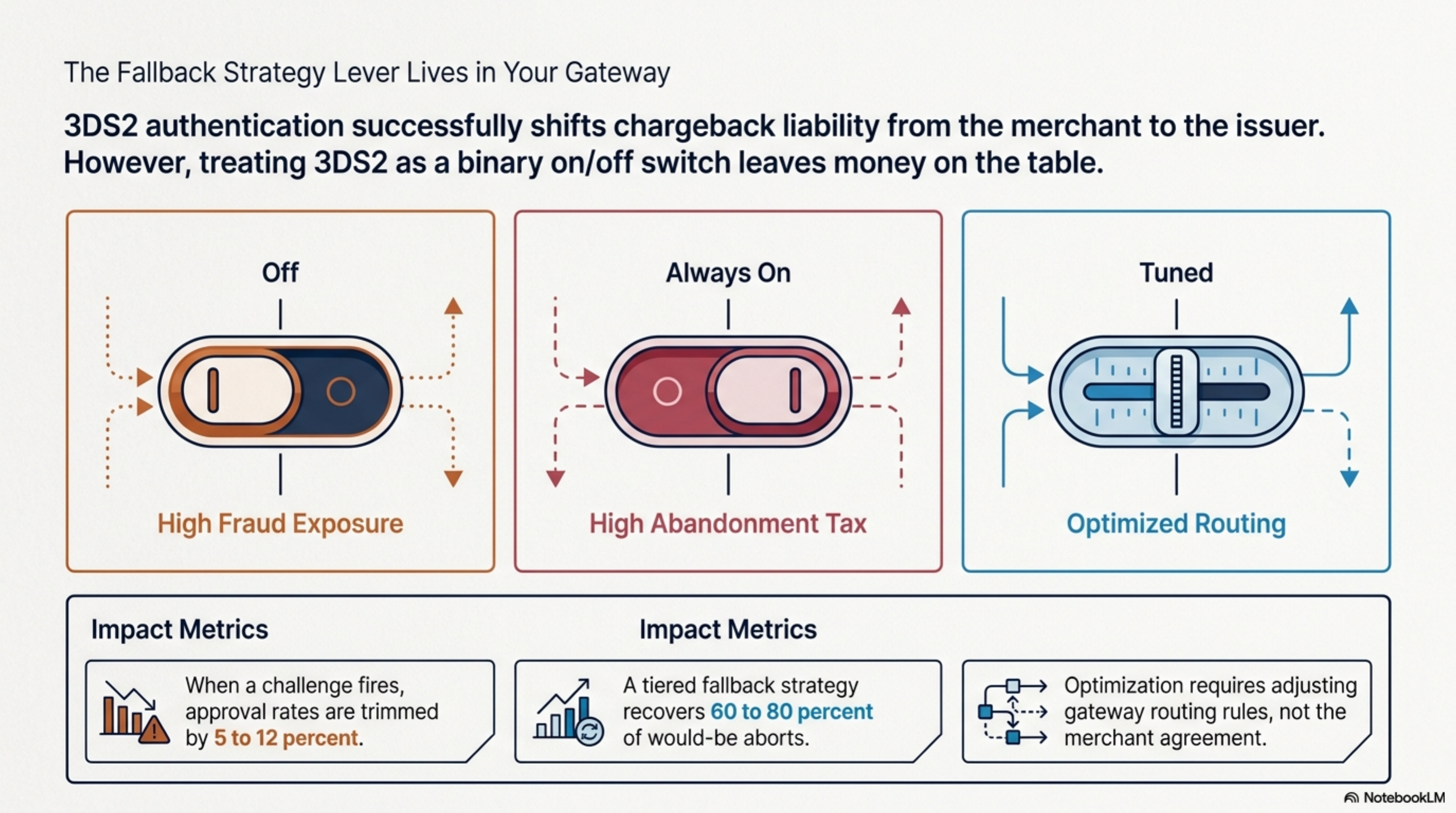
3DS2 authentication shifts chargeback liability to the issuer but trims approval rates by 5 to 12 percent when a challenge fires. Treating 3DS2 as a binary on or off switch leaves money on the table. A tiered fallback strategy, frictionless first, exemptions second, soft-decline retry third, 3DS1 only when forced, recovers 60 to 80 percent of would-be aborts without giving up the liability shift. The lever lives in your gateway routing rules, not the merchant agreement.
What this actually is
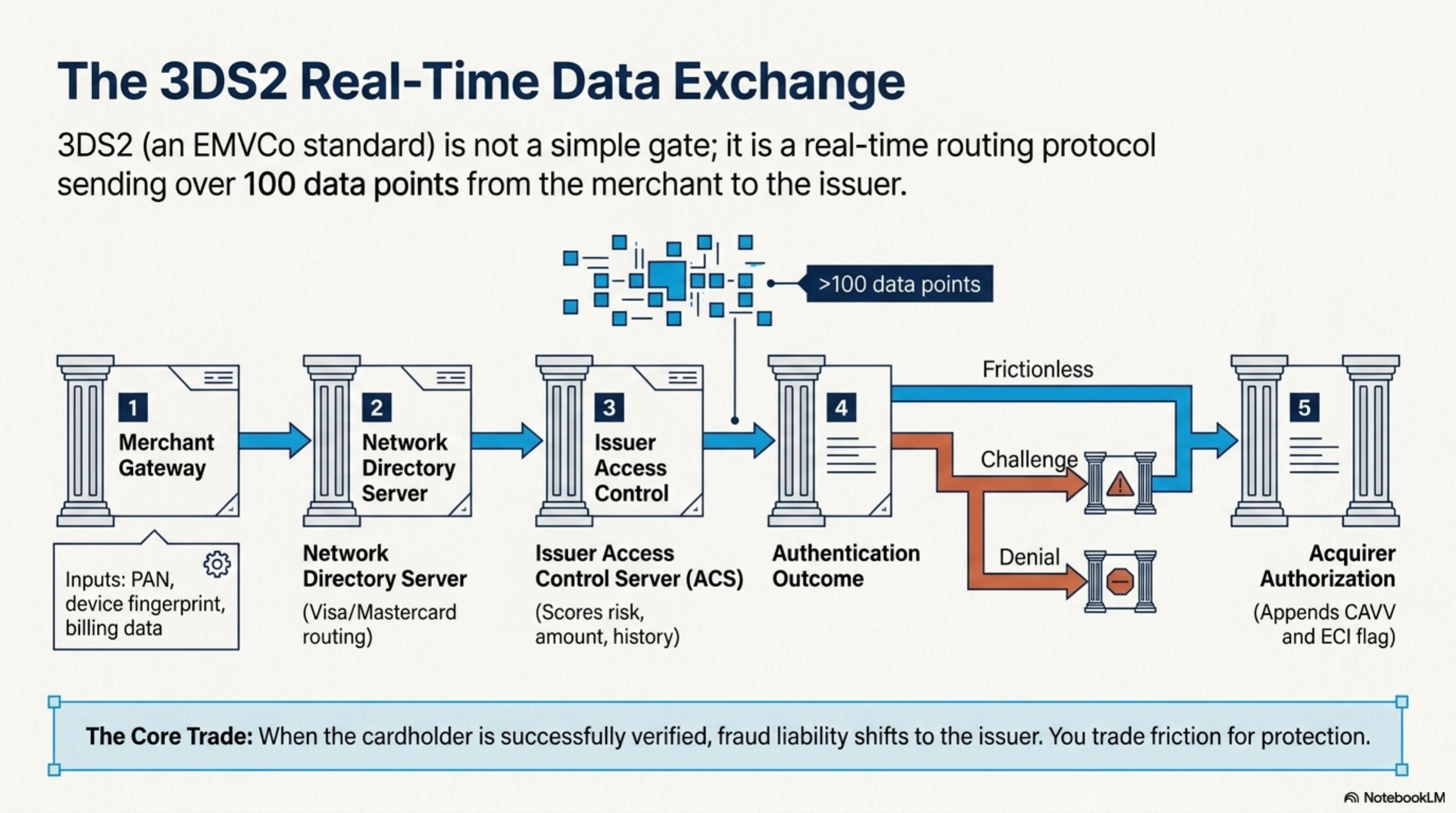
3DS2, the second generation of the 3-D Secure protocol, is the EMVCo standard that authenticates a cardholder during a card-not-present transaction. EMVCo is the joint body formed by Visa, Mastercard, American Express, Discover, JCB, and UnionPay. The protocol routes more than 100 data points from the merchant to the issuer through a Directory Server, letting the issuer score the transaction in real time and decide whether to approve it without challenging the buyer (frictionless flow) or to request a step-up (challenge flow).
The Federal Reserve tracks card-not-present growth and chargeback exposure in its payments research, both of which sit at the heart of why 3DS2 matters at the operator level (see Federal Reserve payments data). Visa documents the protocol and its rules inside its core regulations (see Visa regulations and fees). Mastercard publishes its equivalent under Identity Check, the branded implementation of 3DS2 (see Mastercard interchange and rules).
Liability is the lever. When a 3DS2 transaction is authenticated successfully, fraud chargebacks generally shift from the merchant to the issuer for Visa, Mastercard, Amex, and Discover. That is the trade the protocol offers: lower fraud loss, at the cost of friction that can cost approvals. PSD2 makes 3DS2 mandatory inside the European Economic Area. In the United States there is no equivalent mandate, so US merchants choose when and how to invoke it. That choice is the entire fallback strategy.
3DS2 is a real-time data exchange between merchant, card network, and issuer that authenticates a cardholder and shifts fraud liability to the issuer when the cardholder is verified.
How it works under the hood
A 3DS2 authentication flow runs in five steps:
- The merchant's gateway initiates 3DS2 by sending the cardholder's PAN, device fingerprint, billing data, and around 100 other data points to the Directory Server operated by the relevant card network.
- The Directory Server routes the request to the issuer's Access Control Server (ACS).
- The ACS scores the request using its own fraud models plus the data the merchant supplied. Risk score, transaction amount, prior history, and device reputation are the heaviest signals.
- The ACS returns one of three outcomes: frictionless approval (no buyer interaction), challenge (the buyer completes a one-time passcode or biometric step), or denial.
- If authenticated, the merchant submits the authorization with a CAVV (cardholder authentication verification value) and an ECI flag that tells the acquirer the transaction was 3DS2 authenticated.
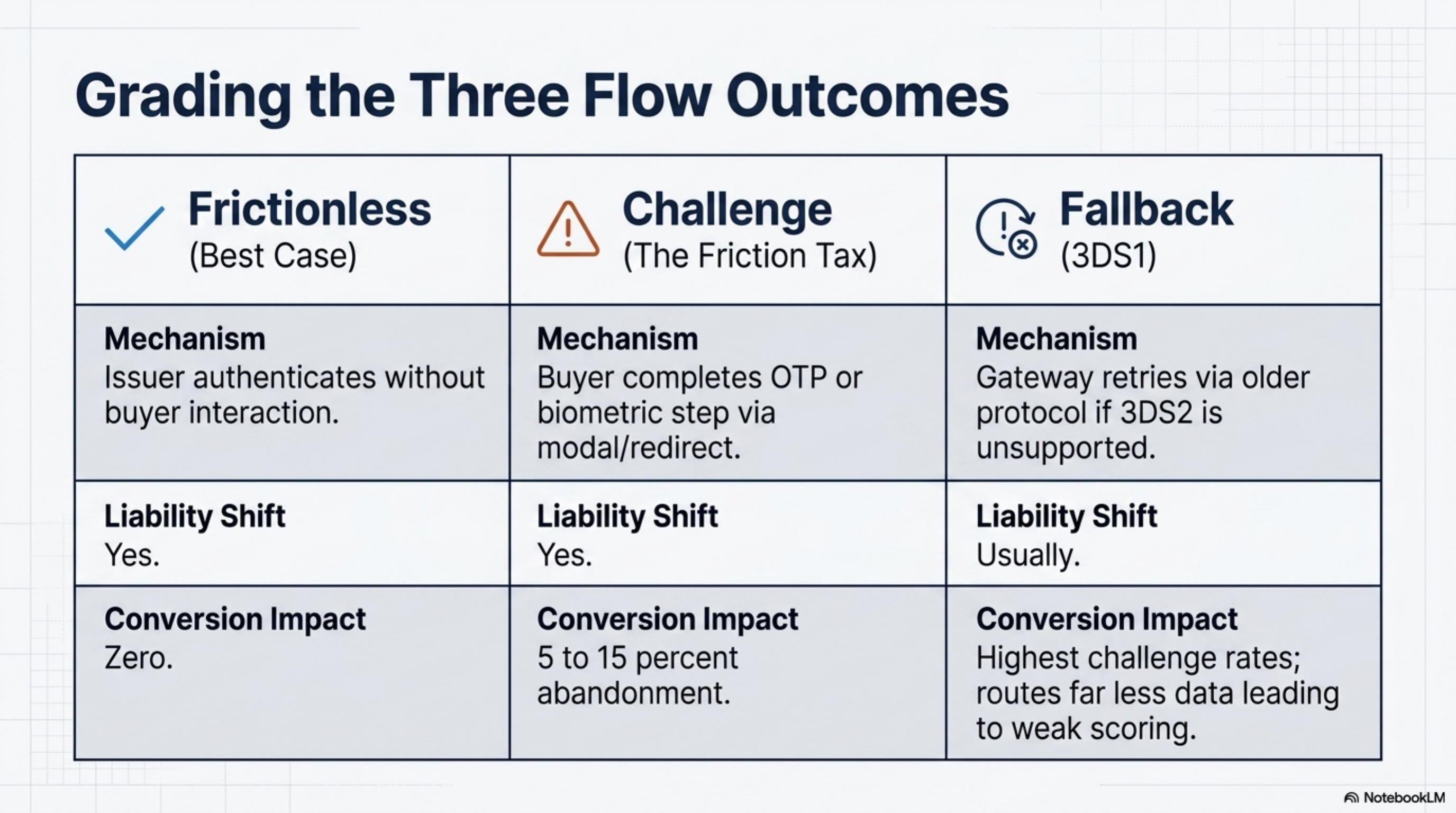
Three flow outcomes drive approval rate math:
- Frictionless: the issuer authenticates without challenging the buyer. Conversion stays high, liability shifts to the issuer. Best case.
- Challenge: the buyer is asked to authenticate, typically in a modal or redirect, with a passcode or app push. Abandonment runs 5 to 15 percent depending on geography and device.
- Fallback: the issuer or the buyer's card does not support 3DS2. The gateway can retry the transaction using 3DS1, attempt the authorization without 3DS, or decline. 3DS1 still carries liability shift on most networks but routes far less data and challenges more often.
Two regulatory regimes shape how often each path fires. PSD2 strong customer authentication (SCA) is mandated for European Economic Area issuers and acquirers, so any EU cardholder buying from a US merchant triggers 3DS2 by default. Inside the US there is no SCA mandate. Issuers and merchants run 3DS2 selectively, usually on high-risk transactions or above defined dollar thresholds.
Soft-decline response codes are not refusals. Visa response code 1A and Mastercard response code 65 both mean the issuer wants 3DS2 before approving. Treating these as hard declines is the single most common configuration error we see on statements at $500K-plus monthly CNP volume.
This is where the fallback strategy lives. A merchant that hard-codes 3DS2 on every transaction pays a conversion tax that PSD2 forces in the EU but does not apply in the US. A merchant that turns 3DS2 off entirely loses the liability shift and absorbs more fraud chargebacks. The correct configuration sits between the two, tuned to card mix, fraud rate, and average ticket.
Where it goes wrong for operators
Four patterns burn merchants who do not tune their 3DS2 fallback logic.
The silent 3DS1 fallback. When a non-3DS2-enrolled card hits a 3DS2-only flow, many gateways fall back to 3DS1 automatically. 3DS1 routes fewer data points, so issuer fraud scoring is weaker, challenge rates climb, and you absorb more abandonment. At $300,000 monthly card-not-present volume with a $120 average ticket, an extra 4 percent abandonment on the 3DS1 fallback bucket costs roughly $12,000 a month in lost revenue if that bucket represents 30 percent of your traffic.
The exemption you never asked for. Visa and Mastercard both publish exemptions that let merchants skip 3DS2 while keeping or partially keeping liability protection. Low-value (under 30 euro inside EEA, with similar thresholds elsewhere), trusted beneficiary (the buyer whitelists you with their issuer), merchant-initiated transactions, and transaction risk analysis (TRA, where the acquirer's overall fraud rate qualifies) are the four. Most gateways do not request them by default. You have to enable them per BIN range or per use case.
The soft-decline blind spot. A PSD2 soft decline (response code 1A on Visa, 65 on Mastercard) means the issuer wants 3DS2 before they will approve. If your gateway treats this as a hard decline and dumps the cart, you lose every one. Retry-with-3DS2 logic recovers 30 to 60 percent of those declines on most platforms.
The contract clause that backloads the cost. Some processors quote a 3DS2 transaction fee of three to seven cents on top of interchange. If your gateway issues 3DS2 on every transaction (frictionless or not), that fee runs on 100 percent of CNP volume. At $1 million monthly CNP volume with an $80 ticket, you process 12,500 transactions. A 5-cent 3DS2 fee on every one adds $625 a month, $7,500 a year, with no liability benefit on the frictionless transactions you would have gotten without 3DS2.
Some processors bundle a flat "authentication fee" into their CNP rate, then bill the network's 3DS2 fee separately as a pass-through. Read the addenda. If both line items appear on the same statement, you are paying the markup twice.
These four patterns each have a different fix. The shared lever is tuning the gateway, not switching processors.
Worked example with real numbers
Consider a US-based DTC apparel brand at $1.2 million monthly card-not-present volume, $95 average ticket, currently on a flat-rate plan at 2.9 percent plus 30 cents. Roughly 18 percent of their volume comes from EU cardholders (PSD2-mandated 3DS2), 82 percent from US cardholders (3DS2 optional). Their current approval rate is 87 percent, with a fraud chargeback rate of 0.18 percent of card-not-present volume.
The math on a blanket 3DS2-on-all-transactions policy:
- 12,632 transactions a month
- 5 percent challenge abandonment on US traffic: 12,632 x 0.82 x 0.05 = 518 lost transactions
- Lost revenue at $95 ticket: $49,200 a month, $590,000 annualized
The same DTC apparel brand, after tuning fallback rules: keep 3DS2 mandatory for EU cardholders (PSD2 requirement). Apply TRA exemption for US tickets under $250 with a low gateway risk score, which covers roughly 70 percent of US volume. Route 3DS2 only on US tickets above $250 or those flagged by the gateway's risk score. Configure soft-decline retry on every response code 1A.
After tuning, the merchant runs 3DS2 challenge on roughly 30 percent of US traffic instead of 100 percent. Estimated abandonment recovery: 350 of the 518 lost transactions, or about $33,250 a month, $399,000 a year. Fraud chargeback exposure rises slightly because more US transactions are unauthenticated. Modeled increase: 0.18 percent to 0.24 percent on the US bucket. At an $80 chargeback fee plus the transaction amount averaged, the extra fraud cost is roughly $1,400 a month. Net benefit: $33,250 saved on lost approvals minus $1,400 in extra fraud equals $31,850 a month, $382,000 a year, from gateway configuration alone.
This math assumes the merchant's fraud rate stays below the TRA threshold published by the card networks. The Nilson Report tracks card fraud loss benchmarks by region and merchant category, which is the right comparable to confirm your fraud rate qualifies (see Nilson Report). If fraud loss runs above 0.13 percent on transactions under 100 euro, TRA exemption is not available and the math shifts toward more 3DS2 invocation, not less.
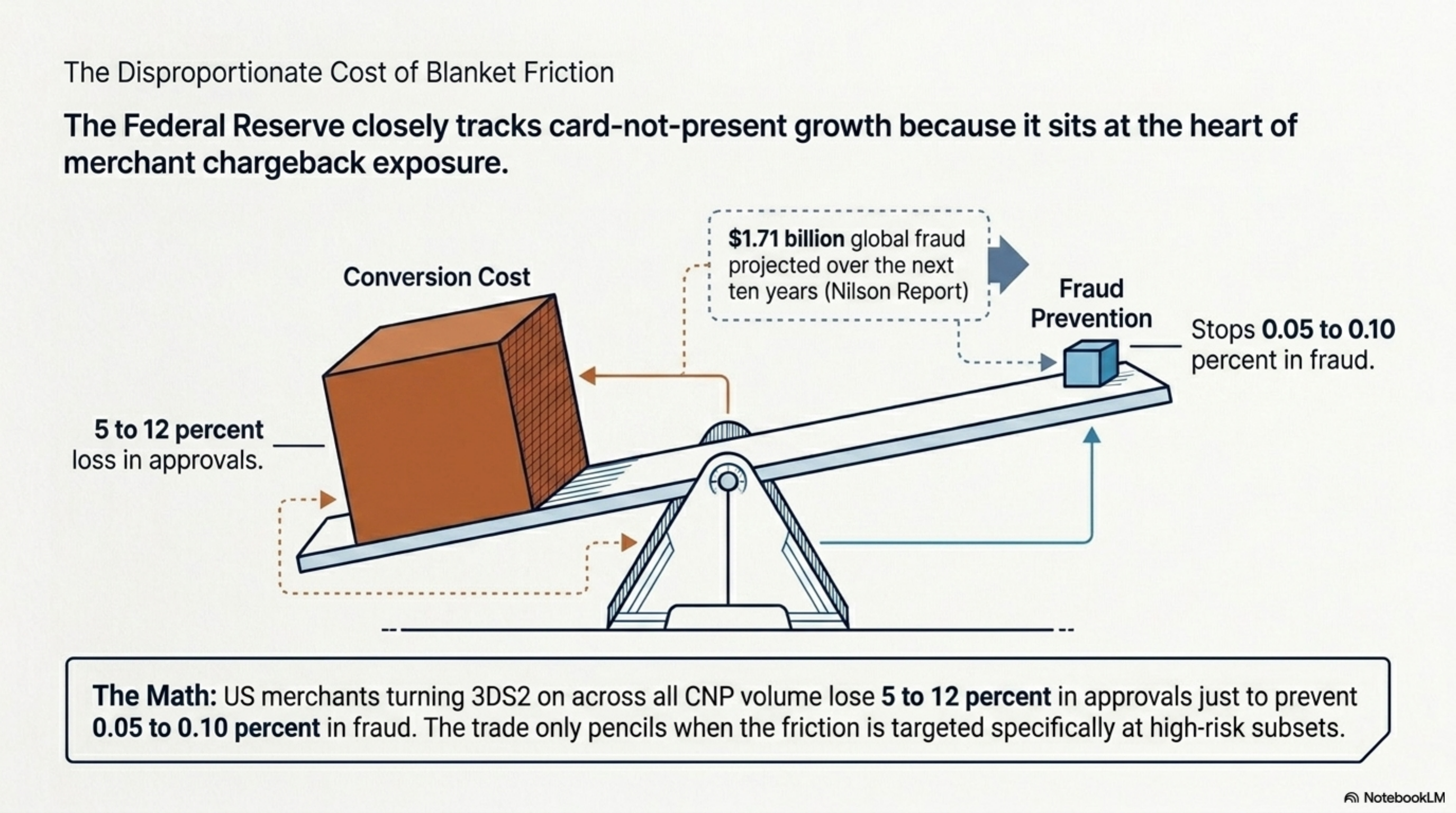
Most US merchants that turn 3DS2 on across all CNP volume lose 5 to 12 percent in approvals to prevent 0.05 to 0.10 percent in fraud. The trade only pencils when you target the high-risk subset.
Operator playbook
- Pull a 90-day report from your gateway segmented by 3DS2 outcome. You need volumes, conversion, and chargeback rate for: frictionless approved, challenge approved, challenge abandoned, 3DS1 fallback, and no 3DS attempted. If your gateway will not give you this split, that is the first thing to fix.
- Identify your EEA cardholder bucket by BIN. Anything issued by an EEA bank requires 3DS2 under PSD2 SCA. Lock those down at 100 percent 3DS2 enforcement. There is no fallback strategy for that bucket.
- For US cardholders, enable TRA exemption requests at the gateway for low-risk transactions under your AOV times two. Most major gateways (Stripe, Adyen, Braintree, Cybersource) support this through a flag in the authorization request. Read the docs, do not assume default behavior.
- Configure soft-decline retry. A response code 1A on Visa or 65 on Mastercard is the issuer asking for 3DS2. Your gateway should retry that transaction with 3DS2 invoked, not dump the cart. Confirm in writing with your processor that soft-decline retry is enabled.
- Audit the 3DS2 fee on your statement. Look for line items like "3DS2 transaction fee," "3DS authentication fee," or "ACS fee." If you are paying more than two cents per attempt and you have 3DS2 on every transaction, calculate the annualized cost and ask the processor to waive frictionless-only fees.
- Push first-party data accuracy at checkout. Matching billing address, persistent device ID, account age, and email reputation all raise your TRA qualification rate. Make sure your checkout passes every data point the gateway accepts.
- A/B test 3DS2 on US tickets between $100 and $300. Most merchants find a threshold where the conversion lift from skipping 3DS2 outweighs the fraud exposure. Run 30-day windows and measure both approvals and chargebacks.
- Renegotiate the 3DS2 line item at contract renewal. If your processor cannot give you per-flow pricing (charge only on challenge, not on frictionless), that is a quote worth running against competitors.