TL;DR
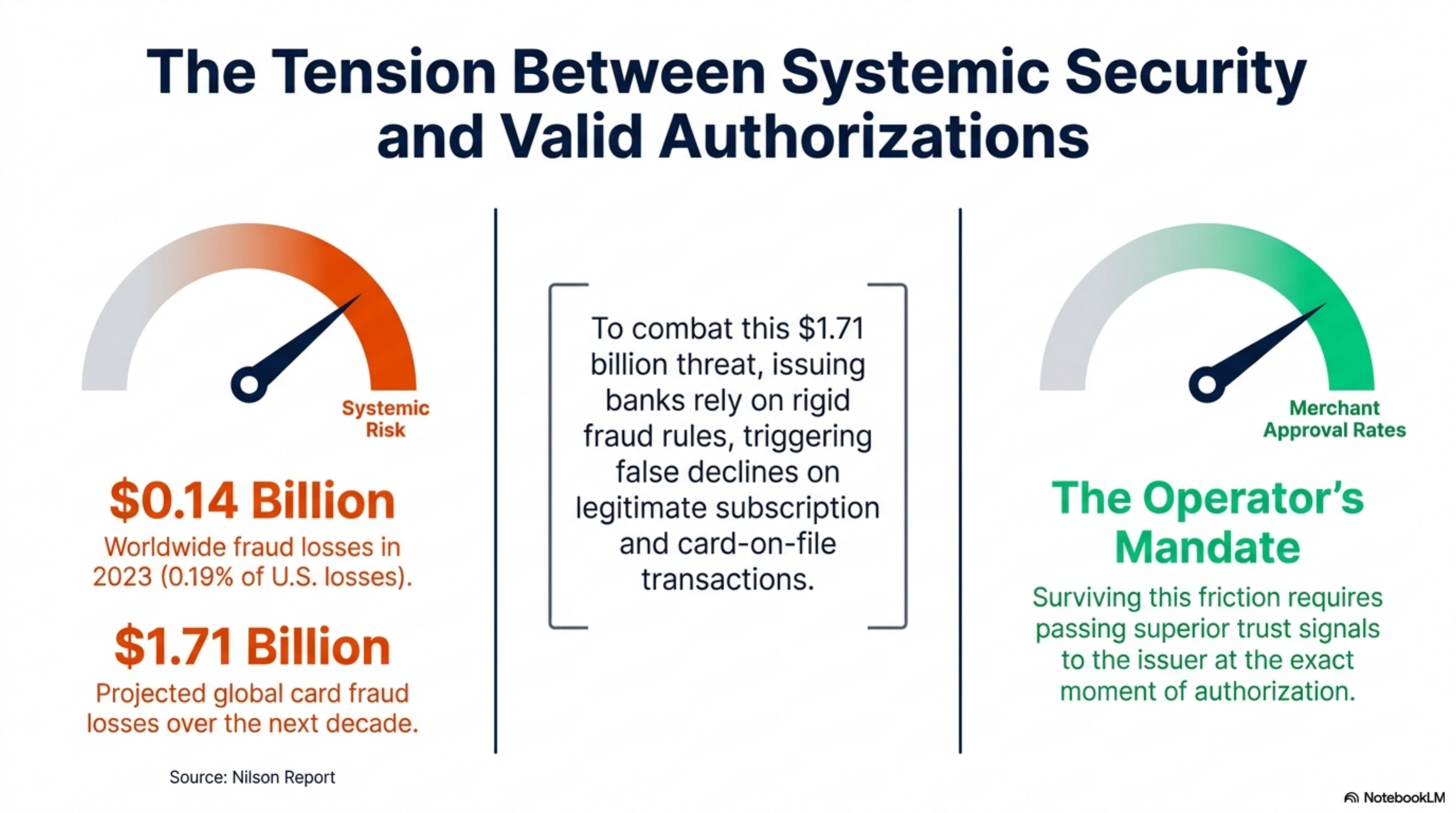
Network tokens replace a cardholder's 16-digit number with an issuer-linked token that auto-updates when a card is reissued. Visa and Mastercard report 2 to 6 percent higher authorization rates on tokenized transactions versus raw card numbers. Subscription, marketplace, and stored-credential merchants capture most of that lift. If your processor charges per-token fees or only stores its own vault tokens, you are leaving approval rate on the table. Pull your monthly authorization report and check decline codes 05, 14, and 54 before you call sales.
What this actually is
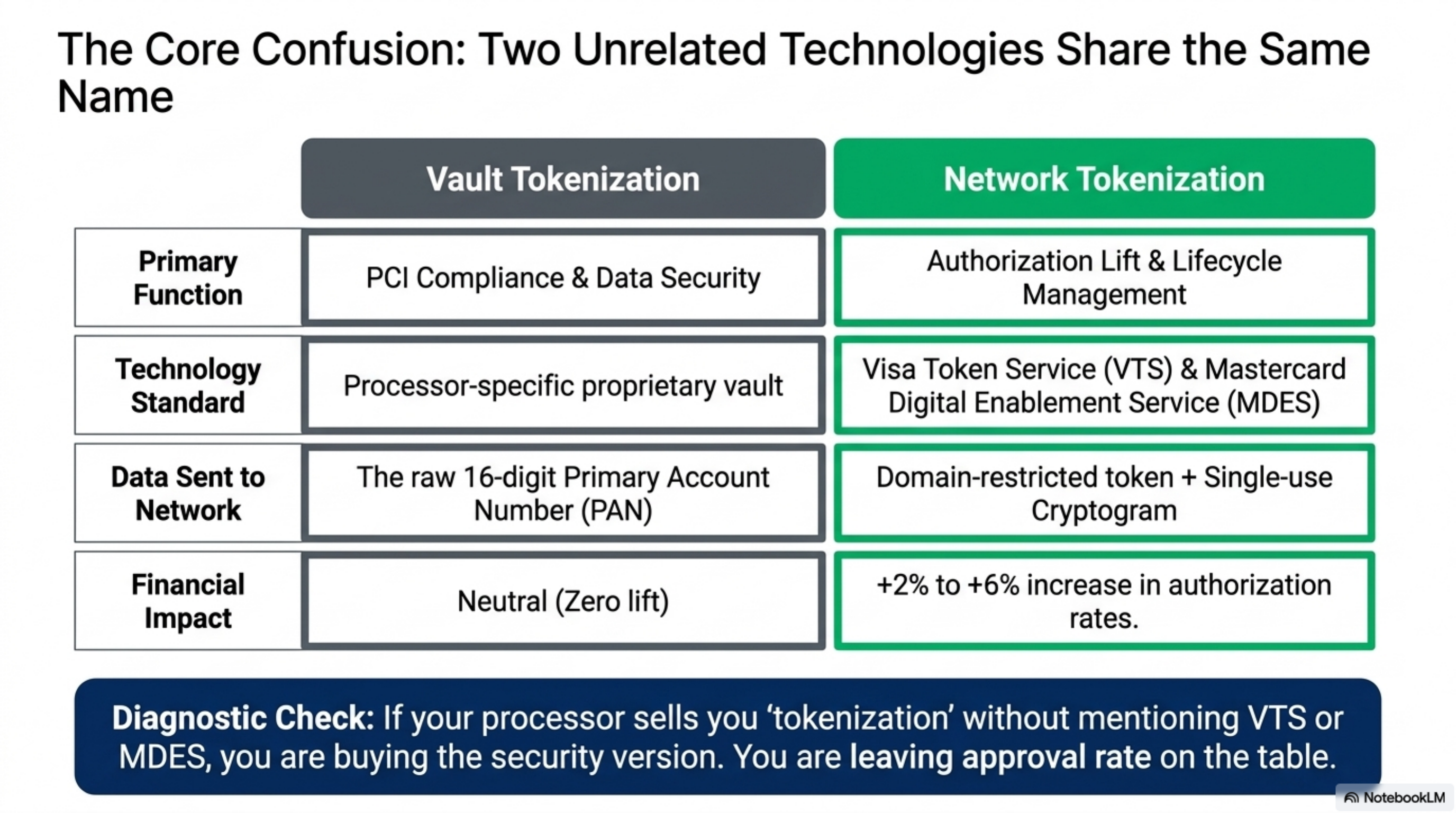
Two unrelated things both get called tokenization, and the difference matters for approval rates.
The first is processor vault tokenization. Your gateway or processor takes the customer's primary account number, stores it in a PCI-compliant vault, and hands you back a random string. Every charge you submit references that string. The PAN never touches your servers. This is a security control. It does nothing for approval rates because the processor still submits the raw PAN to the network at authorization time.
The second is network tokenization. Visa Token Service (VTS) and Mastercard Digital Enablement Service (MDES) sit between the processor and the issuer. The network requests a token from the issuing bank, the issuer returns a domain-restricted token bound to your merchant ID, and every authorization carries a one-time cryptogram in addition to the token. The Federal Reserve's payment systems documentation classifies these as a separate credential type from the funding PAN.
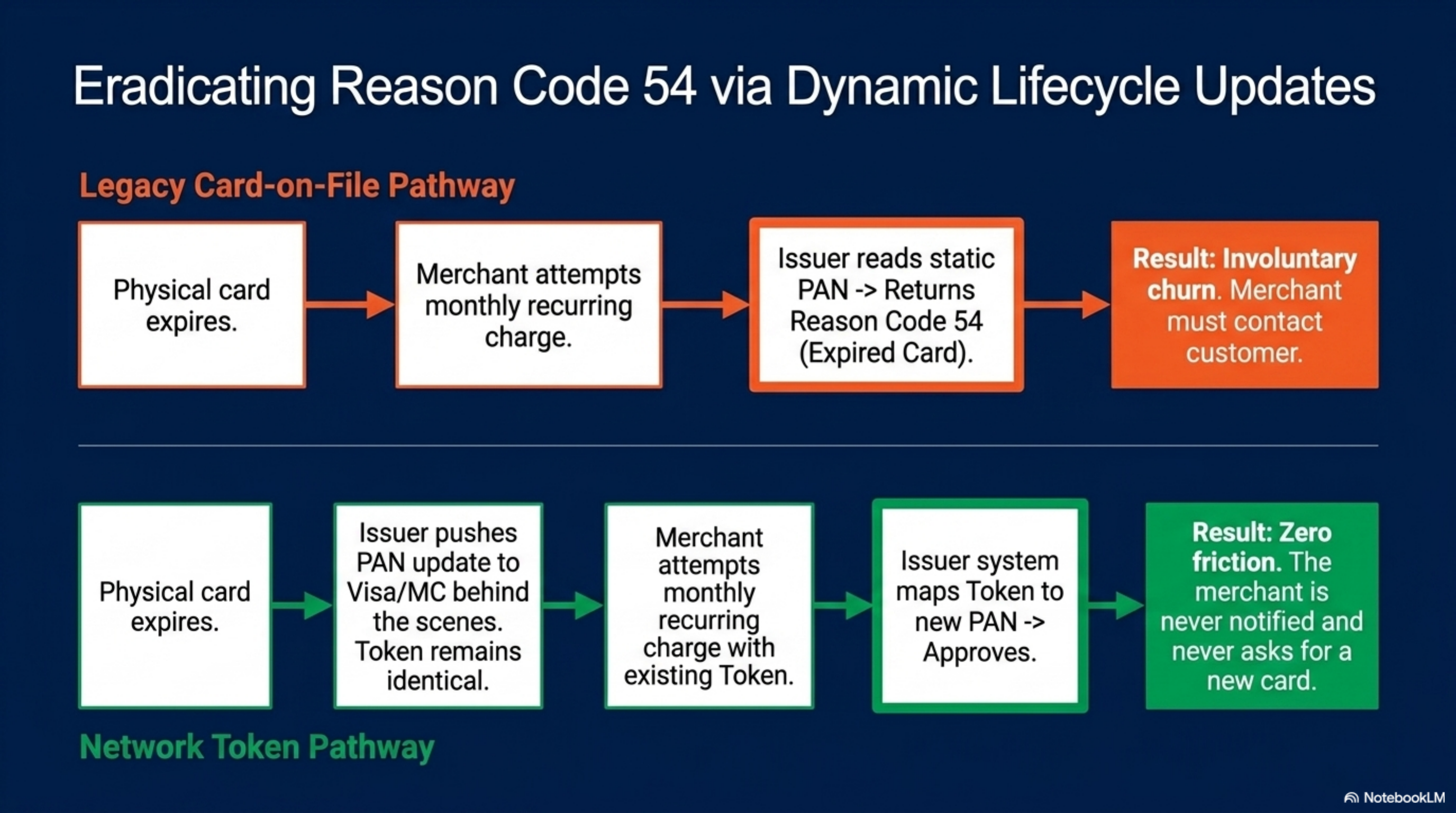
The lift comes from two mechanisms. Issuers treat network tokens as higher-trust because the cryptogram proves the request originated from an authorized merchant. And when a card is lost, stolen, or expires, the underlying PAN changes but the token remains valid: the issuer updates the linkage on its side. The merchant never sees the new number, never asks the customer for a new card, and never takes a decline for reason code 54 (expired card).
Network tokenization replaces a cardholder's 16-digit account number with an issuer-linked token that updates automatically when the card is reissued, raising authorization approval rates.
How it works under the hood
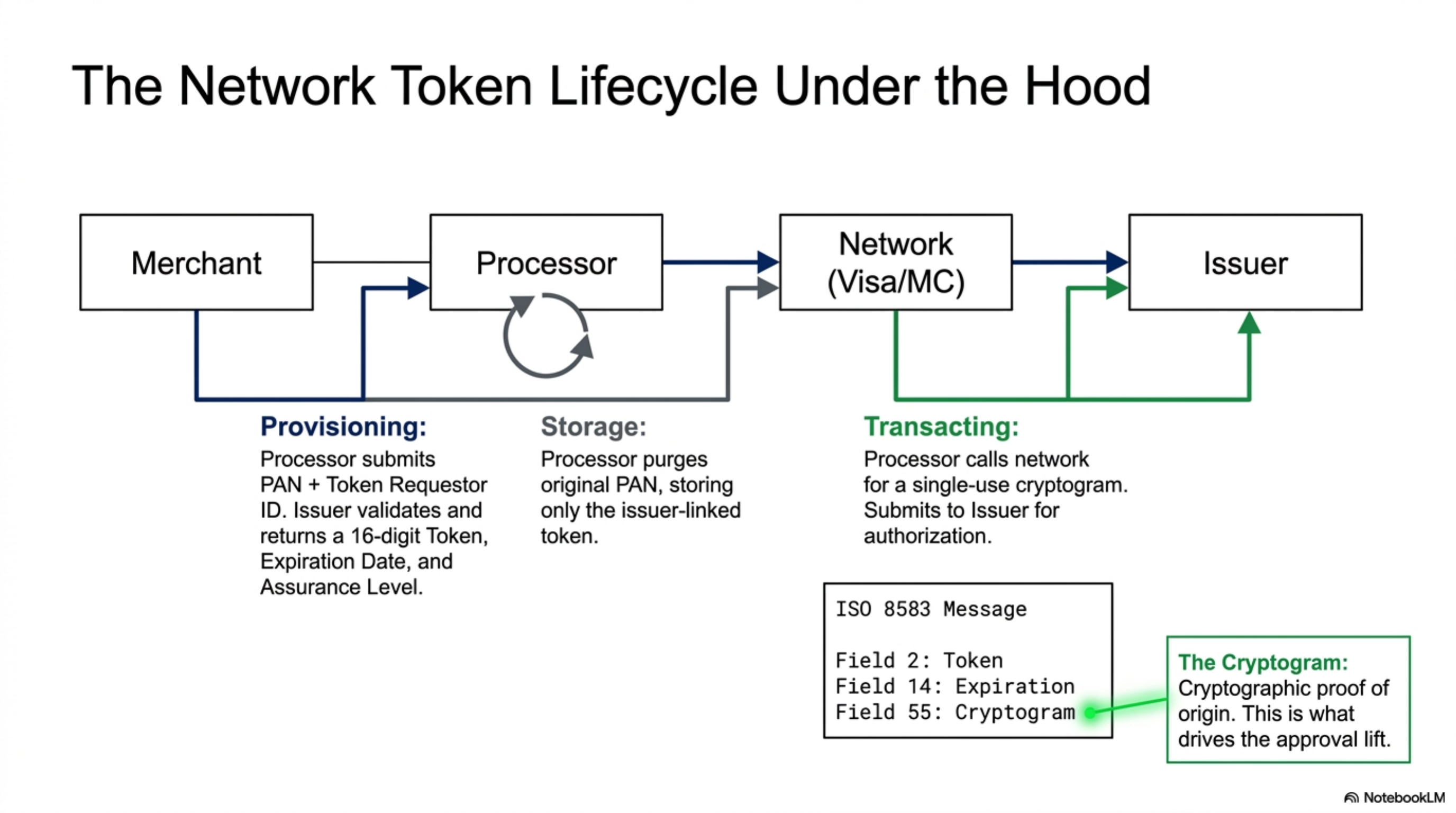
The token lifecycle has three phases: provisioning, transacting, and updating. Each phase involves a different counterparty and a different message format.
- Provisioning request. Your processor sends the PAN, expiration date, and your Token Requestor ID to Visa or Mastercard. This usually happens the first time a customer's card is charged, or when you migrate an existing vault in bulk.
- Issuer check. The network forwards the request to the issuing bank. The issuer confirms the card is in good standing and returns a token (a 16-digit number that resembles a PAN but is not one), a token expiration date, and a Token Assurance Level score reflecting how confident the issuer is in the device or merchant relationship.
- Token storage. Your processor stores the token. The original PAN is purged from your vault, or marked as legacy and held only for fallback. Best practice is to delete the PAN once the token activates.
- Authorization with cryptogram. On each charge, the processor calls the network and receives a single-use cryptogram bound to that specific transaction. The cryptogram plus token goes into the ISO 8583 auth message in fields 2, 14, and 55.
- Issuer authorization. The issuer's auth system recognizes the token as a stored credential, validates the cryptogram, checks available balance, and approves or declines.
- Lifecycle events. If the customer reports the card lost or the card expires, the issuer pushes an update to the network. The next authorization for that token routes against the new PAN automatically. The merchant is not notified and does not need to be.
The published rates Visa and Mastercard set for tokenized credentials sit inside the Visa Interchange Reimbursement Fees schedule and the Mastercard Interchange Rates tables. For most card-not-present categories, tokenized transactions qualify for the same rate as a successful 3-D Secure authentication, typically 5 to 15 basis points below the equivalent non-tokenized CNP rate.
Two operator-relevant details: the token is restricted to the requesting merchant's domain, so a token issued for Merchant A cannot be replayed at Merchant B. And the cryptogram is single-use, so a stolen token without a fresh cryptogram is worthless.
Where it goes wrong for operators
Four patterns show up across statement reviews.
Pattern 1: Per-token fees that erase the lift. Some processors charge 5 to 7 cents per token provisioning call, plus a fractional cent per cryptogram request. A merchant with 12,000 monthly card-on-file customers and 4 to 5 charges each can spend $3,000 to $4,500 a year on token infrastructure. If the approval lift is only 1.5 percent at a $50 average ticket, the math gets close. Negotiate token provisioning into the gateway monthly fee, or push for $0 per cryptogram.
Pattern 2: Vault token sold as network token. Sales reps conflate the two. The contract says "tokenization included," but the technical documentation only references the processor's PCI vault. Ask in writing whether the processor is a registered Token Requestor with Visa and Mastercard. The list of registered TRs is internal to the networks but any processor that participates will confirm in writing.
Pattern 3: Tokens that do not port. Network tokens are bound to a Token Requestor ID. If you switch processors and your old processor is the TR of record, the tokens die. Some processors agree to a token portability clause; others refuse outright. Nilson Report coverage of processor switching costs flags tokenization lock-in as a top-three reason merchants stay on overpriced gateways.
Pattern 4: Subscription billing without cryptogram. If your recurring billing engine submits the token without the cryptogram (or with a stale one), the issuer treats it as a card-on-file transaction, not a network-tokenized one. The lift evaporates. This usually happens because the recurring engine was built before network tokens existed and nobody updated the integration. Pull a sample of 50 subscription charges and confirm field 55 of the auth message is populated.
Most merchants assume tokenization is a single switch. It is not. It is a multi-counterparty integration with four points where it can silently fail.
Worked example with real numbers
Consider a B2C subscription box merchant:
- Vertical: monthly subscription, physical goods
- Monthly volume: $800,000
- Average ticket: $89
- Monthly transactions: roughly 8,989
- Current authorization rate: 88.4 percent
- Card-on-file ratio: 92 percent of attempted charges
- Current processor: flat-rate, 2.9 percent plus 30 cents
Decline reason analysis from the past 90 days:
- Reason 05 (do not honor): 4.2 percent of attempts
- Reason 14 (invalid card number): 1.8 percent
- Reason 54 (expired card): 3.1 percent
- Reason 51 (insufficient funds): 1.4 percent
- Other: 1.1 percent
Reason 54 is the cleanest win. With network tokens, the issuer updates the PAN behind the token on reissue. That 3.1 percent of monthly declines (about 279 transactions at $89, or $24,830 in monthly volume) recovers almost entirely.
Reason 05 is partially recoverable. Visa's published guidance on tokenized transactions shows issuers approve a meaningful share of borderline (reason 05) declines at higher rates when a valid cryptogram is present. That is another 1.3 percentage points of lift, or roughly 117 transactions and $10,413 in monthly volume.
One detail: this calculation assumes the recurring engine actually submits the cryptogram. Half the time a merchant runs this math, the technical migration has not been completed and the auth message is still going out as legacy card-on-file. Pull a sample auth log and confirm field 55 before celebrating.
The 3.1 percent reason-54 decline rate is typical for a subscription merchant with a 12-month average customer lifetime. Network tokens recover almost all of it.
Operator playbook
Seven actions to take this week.
- Pull a 90-day authorization report. Group declines by reason code. Sum reason codes 05, 14, 51, 54, 65, and 91. These are the network-token-recoverable categories. If the total is above 4 percent of attempts, network tokens are worth the migration cost.
- Confirm Token Requestor status in writing. Email your processor: are you a registered Token Requestor with Visa Token Service and Mastercard MDES, and can you provision and store network tokens for our merchant ID? If the answer is yes, ask for the TR ID. If the answer hedges, you are looking at vault tokens, not network tokens.
- Get the fee schedule in writing. Request line items for: token provisioning fee, per-cryptogram fee, monthly token storage fee, and lifecycle update fee. The first three should be $0 on any reasonable contract. The fourth is sometimes a small monthly bundle.
- Demand a token portability clause. If you switch processors, can the existing tokens transfer to the new TR? Both Visa and Mastercard support portability between certified TRs. Some processors refuse to cooperate. Get a written commitment to participate in a portability request before signing.
- Audit a sample auth message. Ask your processor to pull the raw ISO 8583 messages for 20 random subscription charges. Confirm field 55 (cryptogram) is populated and field 2 (PAN/token) is the token, not the original PAN. This is the single highest-value sanity check.
- Run a 30-day A/B test if you can. Some integrations let you route a percentage of card-on-file traffic through network tokens and compare. A 1.5 percent or higher approval-rate lift inside 30 days is normal. If the lift is below 0.5 percent, the integration is misconfigured.
- Recalculate interchange. Tokenized CNP transactions qualify for the lower CNP-secure interchange tier on both Visa and Mastercard. Pull last month's statement, find the CNP rows, and confirm tokenized volume is hitting the secure rate, not the standard CPS rate. The difference is usually 5 to 15 basis points.